2024-1-23 02:28:49 Author: www.horizon3.ai(查看原文) 阅读量:17 收藏

What is this all about?
Two recent Ivanti CVEs are being actively exploited by suspected nation-state threat actors. The CVEs are as follows:
- CVE-2024-21887: A command injection vulnerability in web components of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure (9.x, 22.x) allows an authenticated administrator to send specially crafted requests and execute arbitrary commands on the appliance. [9.1 Critical]
- CVE-2023-46805: An authentication bypass vulnerability in the web component of Ivanti ICS 9.x, 22.x and Ivanti Policy Secure allows a remote attacker to access restricted resources by bypassing control checks. This vulnerability can be leveraged in conjunction with CVE-2024-21887, a command injection vulnerability. [8.2 High]
According to the CISA KEV Catalog, Ivanti Connect Secure (ICS, formerly known as Pulse Connect Secure) and Ivanti Policy Secure contain a command injection vulnerability in the web components of these products, which can allow an authenticated administrator to send crafted requests to execute code on affected appliances. Both vulnerabilities are being exploited in the wild.
Why does this matter?
In both cases, remote unauthenticated attackers can bypass authentication and execute remote operating system commands to compromise the Connect Secure host.
How do you fix it?
Patches from Ivanti for both issues are expected to be available between January 19 and January 22, 2024. Ivanti shared this workaround while patches are in development.
How to verify you’re not at risk of exploitation?
As of January 17, 2024, Horizon3.ai announced new attack content for both CVEs as part of the latest NodeZero release, which now attempts to exploit these flaws. Running a NodeZero pentest will verify if you are exploitable, and once remediated, you can prove that you are no longer at risk of exploitation. If you’re not a customer, you can start your free trial here.
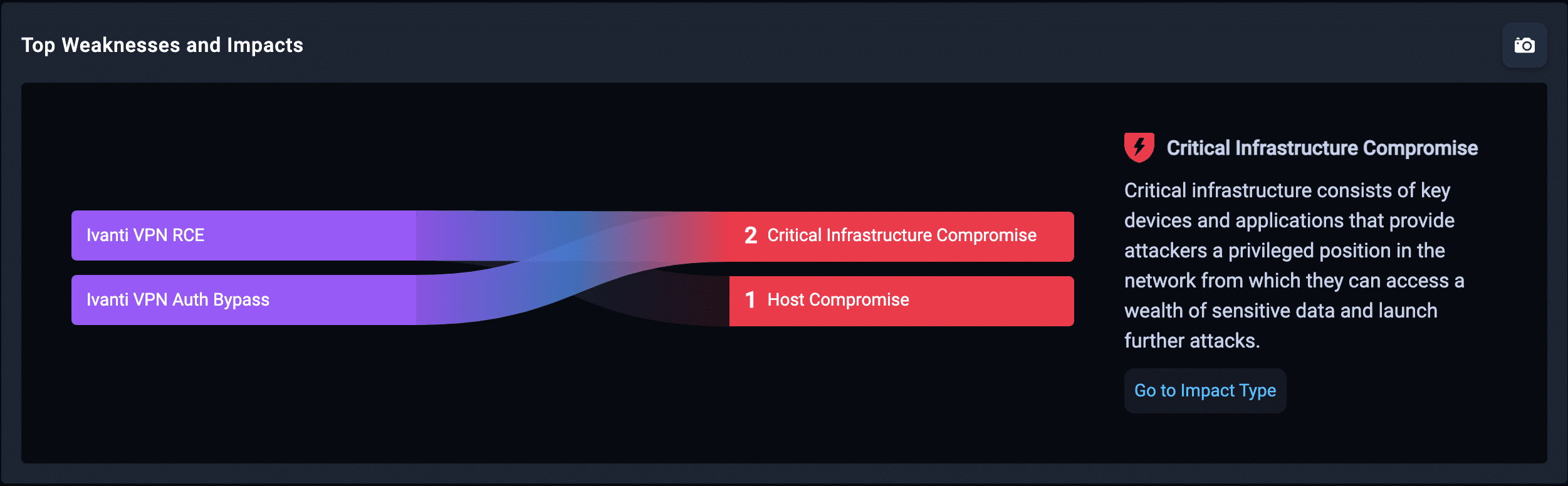
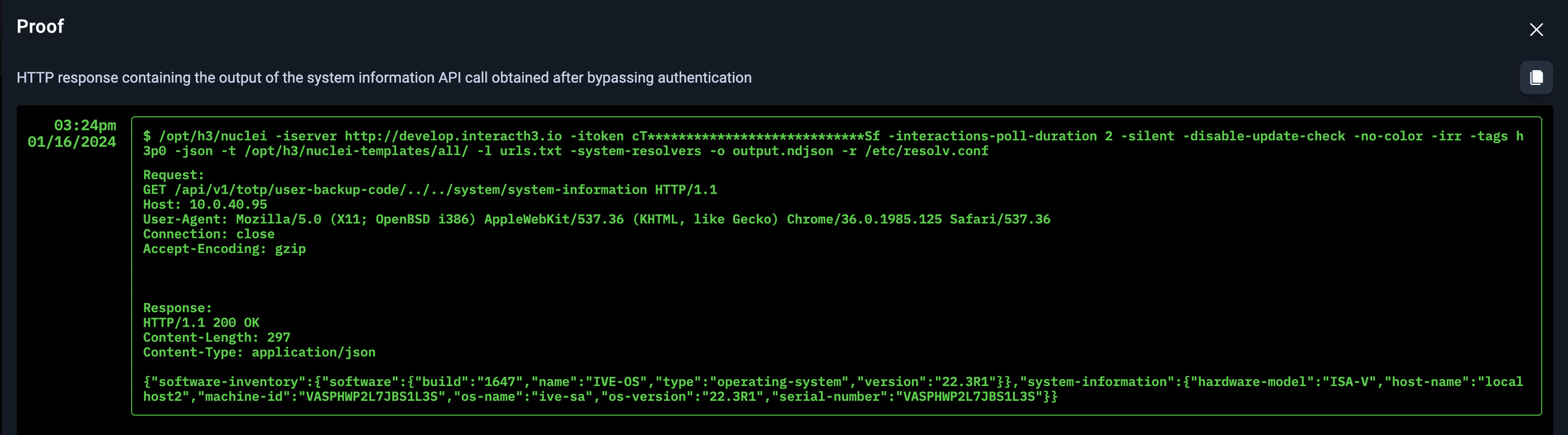
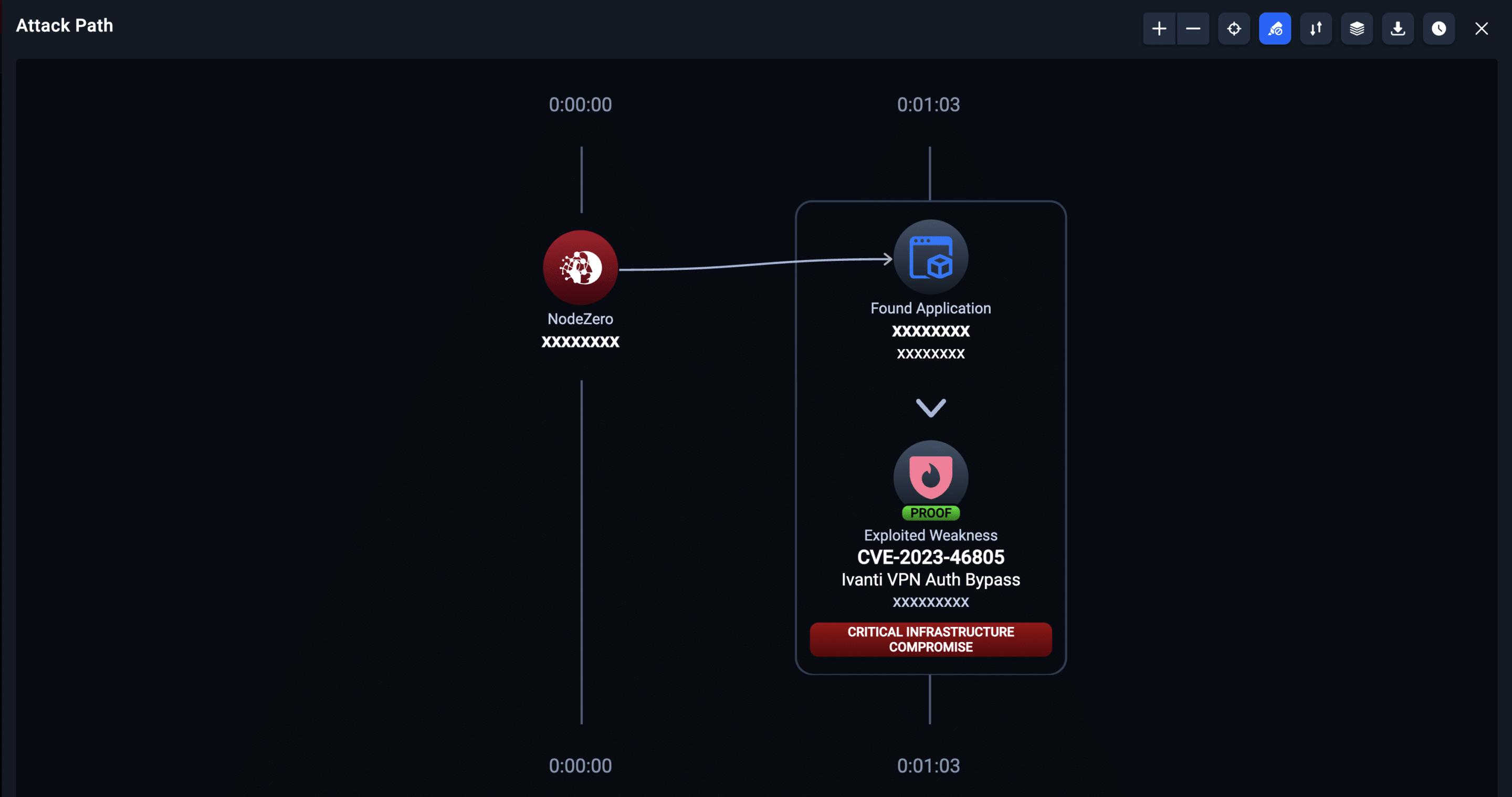
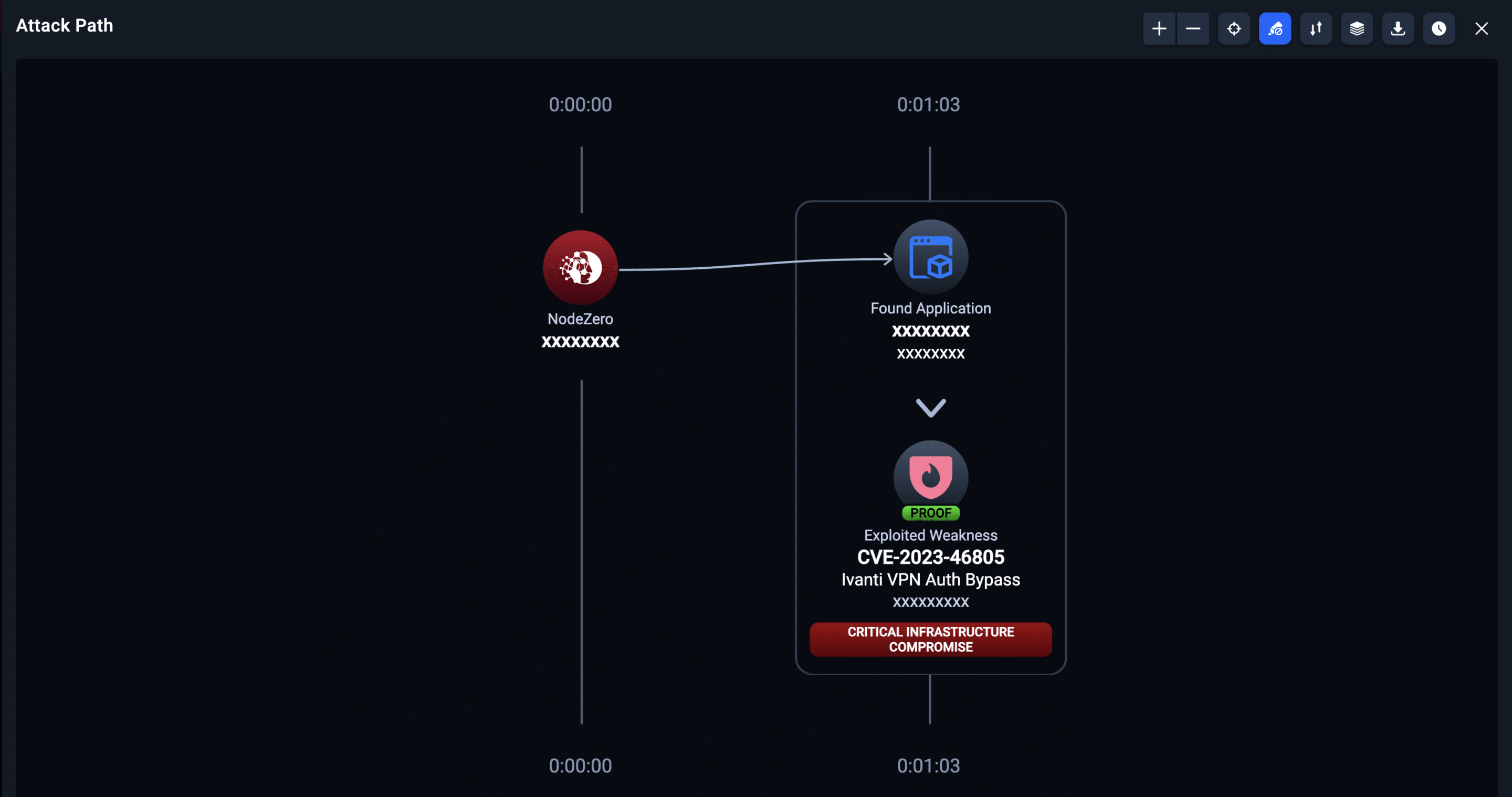
What You’ll See When Running NodeZero if You’re At Risk of Exploitation
(Note: this CVE can be directly exploited in ~60 seconds by an attacker and doesn’t require chaining.)
Additional Details
The Ivanti Connect Secure VPN faced a significant security threat due to two zero-day vulnerabilities identified as CVE-2023-46805 and CVE-2024-21887. Ivanti is preparing a security update to address these vulnerabilities in all supported versions (9.x and 22.x) of Connect Secure and Policy Secure gateways.
The first vulnerability, CVE-2024-21887, is a command injection vulnerability. This particular vulnerability would enable a cyber threat actor to inject and execute arbitrary commands on the system. The second vulnerability, CVE-2023-46805, is an authentication bypass vulnerability. This flaw could potentially allow a cyber threat actor to bypass the standard authentication processes of the system. These vulnerabilities posed a significant risk as they could be exploited to take control of an affected system.
According to Ivanti, “Upon learning of the vulnerability, we immediately mobilized resources and mitigation is available now. Patches will be released in a staggered schedule with the first version targeted to be available to customers the week of 22 January and the final version targeted to be available the week of 19 February.” Also, Ivanti does share a workaround while patches are in development.
Additionally, the Cybersecurity & Infrastructure Security Agency (CISA) emphasized the importance of immediate action, urging users and administrators to review Ivanti’s Knowledge Base article and security update. CISA also included these vulnerabilities in their Known Exploited Vulnerabilities (KEV) Catalog, highlighting the active exploitation and the need for rapid remediation to protect networks against these active threats.
Volexity has identified widespread exploitation of chained vulnerabilities CVE-2024-21887 and CVE-2023-46805. This exploitation has affected thousands of machines and may have infected many more. Volexity’s scan methodology would not have worked against organizations that have already deployed the Ivanti mitigation or had otherwise been taken offline. As a result, Volexity suspects there may likely be a higher number of compromised organizations than identified through scanning (which totaled more than 1,700).
In summary, the Ivanti Connect Secure VPN vulnerabilities represented a critical security risk, with potential for unauthorized access and control over affected systems. Immediate action and ongoing vigilance are essential for mitigating these threats.
For more detailed information and updates, you can refer to the following:
CISA website: https://www.cisa.gov/news-events/alerts/2024/01/10/ivanti-releases-security-update-connect-secure-and-policy-secure-gateways
Volexity’s analysis: https://www.volexity.com/blog/2024/01/10/active-exploitation-of-two-zero-day-vulnerabilities-in-ivanti-connect-secure-vpn/
如有侵权请联系:admin#unsafe.sh